Working with AWS for better healthcare: Announcing the Tableau Server on AWS Healthcare Quick Start
We're excited to announce the Tableau Server on AWS Healthcare Quick Start! Learn how we're working with AWS for better healthcare.
Last week at Tableau Conference we announced an expansion of our partnership with Amazon Web Services (AWS), including a new Tableau Server on AWS Healthcare Quick Start. With common security controls like end-to-end encryption already preconfigured, healthcare customers can now quickly and easily deploy a modern analytics solution that supports their HIPAA compliance programs out of the box.
This Quick Start comes with downloadable AWS CloudFormation templates, a deployment guide, and a jointly authored security controls reference describing how different parts of the HIPAA Security and Privacy rules apply to AWS and Tableau, as well as the specific implementation in this Quick Start, in accordance with the AWS Shared Responsibility model.
Why did we build it?
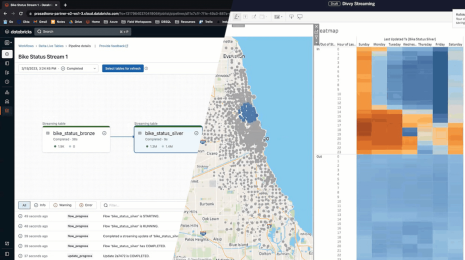
Our healthcare customers across the globe are using analytics to harness the power of their data assets, whether to enable precision medicine, unlock the full value within electronic health records, or improve internal operations. Several of these customers, such as Inova Translational Medicine Institute (ITMI), are increasingly taking advantage of and embracing Tableau on the AWS Cloud for their analytics initiatives.
Given the sensitivity of health data, security is paramount to our healthcare customers. In addition to implementing technical controls (such as encryption in-transit), healthcare organizations that must align to regulatory frameworks, (such as HIPAA,) would have to manually incorporate how Tableau Server fits into their compliance protocols. The additional step(s) can often introduce friction into the process of getting started and affect the speed of deployment, adoption, and ultimately insights and decisions.
We listened to this feedback from our customers and are supporting their journey with this new offering that will simplify how Healthcare organizations can confidently deploy Tableau Server on AWS and support their HIPAA compliance needs. With a few clicks, you can quickly set up Tableau Server in the AWS Cloud, and start securely analyzing your healthcare data. In the section below I will highlight several key security features of this Quick Start and how healthcare organizations can quickly and easily deploy Tableau Server on AWS.
What security constructs does this Quick Start pre-configure?
Building security into the deployment
This Quick Start gives customers the ability to launch Tableau Server in either a new Amazon Virtual Private Cloud (VPC) or an existing VPC.
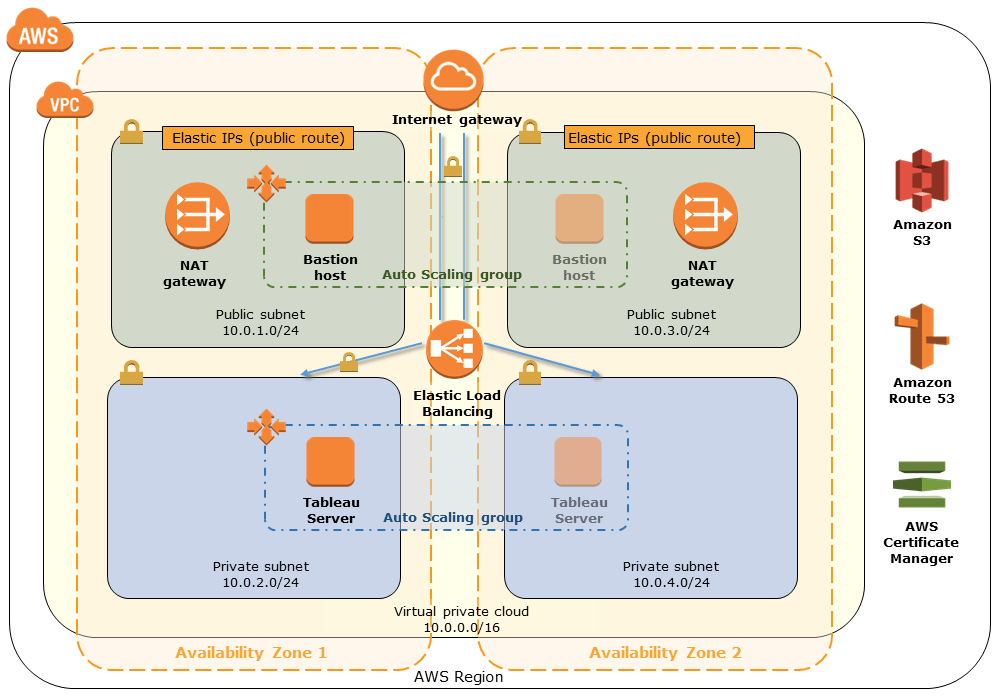
Several security measures within this Quick Start help Tableau customers deploy single-node Tableau Server in their AWS environment and align with their responsibilities to the AWS Business Associates Addendum (BAA) and HIPAA in general.
Server-side encryption at rest
Tableau Server is deployed on Amazon EC2 instances backed by Amazon Elastic Block Store (EBS) volumes. Each EBS volume is encrypted at rest using envelope encryption with AWS Key Management Service (KMS).
Each Tableau Server deployment, which can be either Linux- or Windows-based, is built from a base Amazon Machine Image (AMI). These AMIs have unencrypted root volumes, which means we need to create base AMIs with encrypted EBS. For more on the series of steps detailing how to do this, read the AWS version of this announcement.
Encryption in transit
Covered entities under HIPAA are required to have a Business Associates Addendum with AWS for the analysis of Protected Health Information, or PHI. The AWS BAA mandates that all PHI on AWS be not only encrypted at rest, but also in transit. To remain consistent with the AWS BAA, PHI is first encrypted from the internet to the Application Load Balancer with a SSL certificate stored in AWS Certificate Manager, and then from the Load Balancer to Tableau Server using a self-signed certificate generated by OpenSSL.
To learn more about encryption in transit with Tableau, please see the documentation for Windows and Linux.
Logging and configuration management
AWS Config is often a key component to how healthcare organizations visualize their AWS environment. You can take your policies, translate them into technical controls, and then build AWS Config rules that map to those policies. In this Quick Start, we create several Config rules to demonstrate how one can monitor their Tableau Server environment. These rules are scoped to a specified tag so you can monitor your Tableau resources separately from your other resources.
The following screenshot shows what it looks like after the Quick Start deployment has finished. All Config Rules should show as compliant. For example, the second rule below confirms that your Tableau server deployment has Amazon EBS volumes encrypted at-rest. The fourth confirms that that your load balancer only allows for HTTPS communication. For more on the HIPAA rules this Quick Start addresses, read the Security Controls Reference.

While outside the scope of this Quick Start, you could build additional Config rules, such as checking configuration files on Tableau Server (e.g. the SSL certificate location) using a combination of AWS Lambda and AWS Systems Manager. You can also use additional tagging policies to group additional resources if you wish to broaden the scope of your checks with AWS Config.
Enabling self-service visual analytics with Tableau
Once you have Tableau Server deployed on AWS with pre-configured, HIPAA-related controls, you can start diving into a range of use cases from helping providers identify revenue cycle bottlenecks and improving patient flow in the emergency department, to improving how industry-leading payers can proactively manage high-risk patients.
With the current shift from volume-based to value-based care, healthcare organizations (HCOs) have additional financial imperatives to optimize their operations and ensure patients get the right treatment earlier on in their regimen. Following are two of the many ways HCOs can leverage Tableau to gain new insights into their data sets.
Diving into the opioid crisis
Opioid addiction is one of the biggest public health crises today. The National Institute of Drug Abuse estimates that over 115 people die every day from opioid addiction and this epidemic costs over $78.5B USD. One of the key causes of this epidemic is due to the over-prescription of opioid medications, often due to pain management. With Tableau, you can quickly dive into the details of the epidemic by rapidly interacting with your data sets to understand the severity of opioid overdose compared to other drugs (top right), what specialties are most responsible for prescribing opioids (bottom middle), and dive into the specific physicians prescribing opioids at both high volume and high percentage (bottom left).
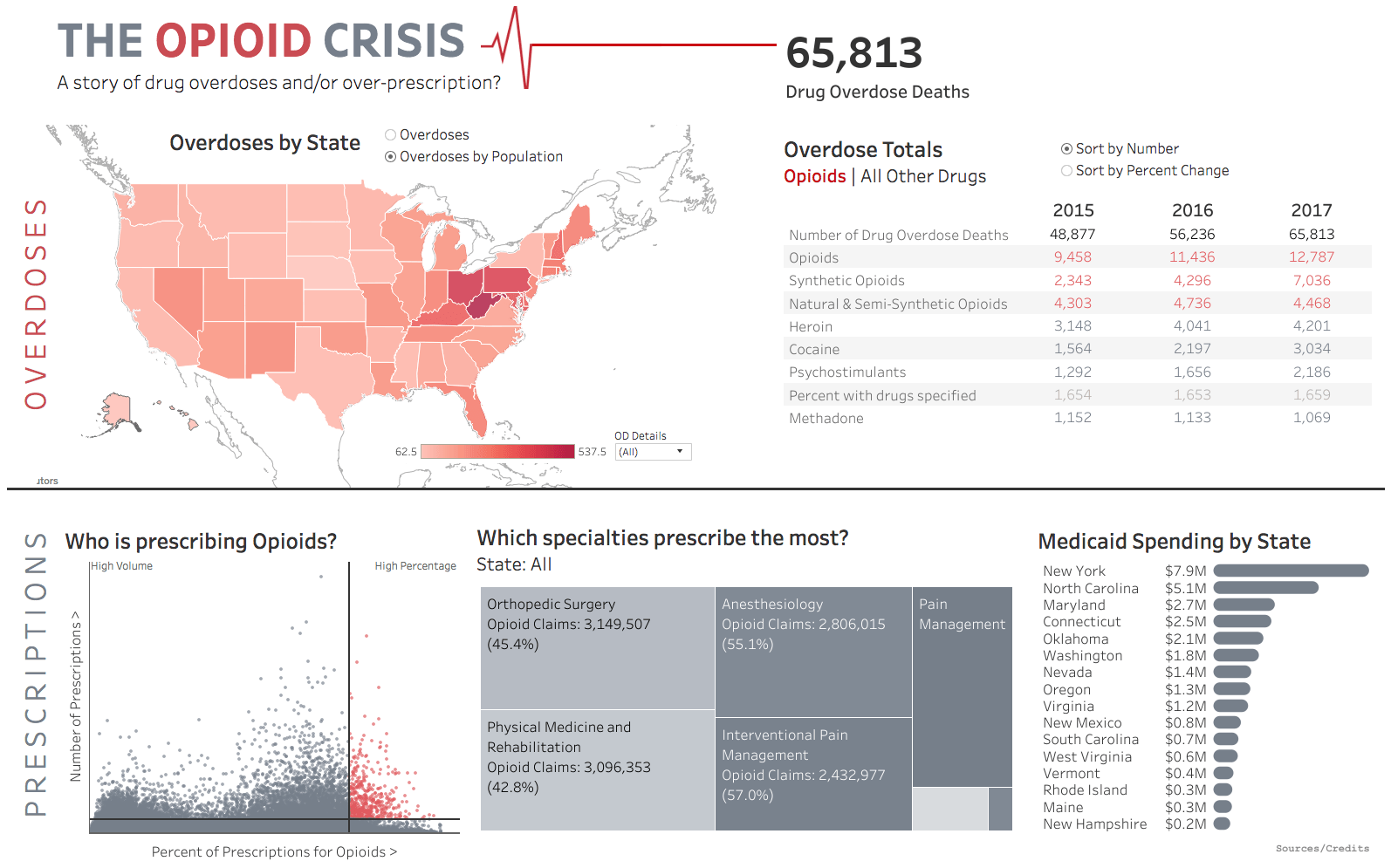
For more information about this use case, please see this Tableau blog post.
Understanding reimbursement
Ensuring that physicians and procedures are driving the desired health outcomes is important for the financial solvency of a healthcare organization. The following dashboard helps provider organizations to better understand a critical metric for these efforts—reimbursement rates. You can visualize the average charge per patient and analyze the reimbursement rate based on attending physician and medical procedure, and adjust how your organization operates to improve outcome-based reimbursement rates.

Whether you are looking to move to the cloud and reduce your on-premises footprint, or you’re interested in a faster and easier way to achieve a HIPAA-compliant analytics platform, this Quick Start will give you the best configuration that’s based on the deep knowledge and real-world deployment experience of our technology experts. Customers can use this reference architecture as a starting point and expand it or configure additional resources to suit their own needs.
We hope this simplifies the process to meet your compliance objectives. With simplicity, you’ll likely have more time and resources to dive into your data and drive self-service analytics empowerment across your organizations.
Getting started
Getting started is easy. Just navigate to the Tableau Server on AWS Healthcare Quick Start page and follow the directions to deploy Tableau Server. Be sure to review the deployment guide and security controls reference to understand how this deployment can help support your healthcare compliance objectives.
- View the architecture and details
- See the deployment guide for step-by-step instructions
- View the security controls reference
- Download the AWS CloudFormation templates that automate the deployment
We look forward to seeing how healthcare organizations use this new Quick Start to analyze their valuable health datasets.
Please note: This Quick Start will not, by itself, make you HIPAA-compliant. The information contained in this Quick Start package is not exhaustive, and must be reviewed, evaluated, assessed, and approved by you in connection with your organization’s particular security features, tools, and configurations.
Learn more about Tableau and AWS
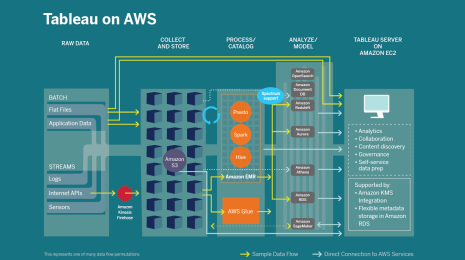
Through our partnership, we're deeply invested in bringing Tableau and AWS technology together so that you can depend on fast and flawless performance for your cloud analytics use cases. The flexibility, scalability, and reliability of the AWS cloud services coupled with the intuitiveness of Tableau’s visual analytics platform provide a modern approach that is both agile and secure. We offer a range of native connectors to AWS services, including Amazon Redshift, Amazon Redshift Spectrum, Amazon Aurora, Amazon Athena, and Amazon EMR.
To learn more about our work with AWS, see the Tableau AWS solutions site. If you're attending AWS re:Invent November 26–30 in Las Vegas, join us at booth #1428 in the Expo Hall located at the Venetian.
Histórias relacionadas
Subscribe to our blog
Receba em sua caixa de entrada as atualizações mais recentes do Tableau.