Tableau Online tips: A security checklist for publishing data to the cloud
Data is crucial to all areas of the business. And for many of us, our data also includes sensitive information. It’s critical that a business’s revenue and customer details, for example, remain private. When published to the cloud, you need to be assured this type of sensitive data remains secure and private. Protecting the security of our users’ data is a top priority at Tableau. If you're considering—or are already working with—data in the cloud, there are specific questions you need to know are met.
Editor’s Note: Tableau Online is now Tableau Cloud.
This post is part of a series covering tips, tricks, and ideas on Tableau Online, our cloud collaboration and sharing platform.
Data is crucial to all areas of the business. And for many of us, our data also includes sensitive information. It’s critical that a business’s revenue and customer details, for example, remain private. When published to the cloud, you need to be assured this type of sensitive data remains secure and private. Protecting the security of our users’ data is a top priority at Tableau. If you're considering—or are already working with—data in the cloud, there are specific questions you need to know are met: Who can access my data? How can I be confident my data will remain secure? What is my provider’s privacy policy? Here at Tableau, my team is responsible for ensuring these questions are answered. To holistically understand security in the cloud, it’s important to consider the following four key aspects of security for hosted solutions:
1. Operational Security
Saying we do the right thing isn’t enough. To ensure our customers feel safe trusting us with their data, Tableau is audited by independent third parties throughout the year. As a public company, our SOX audits cover identity management, change control, and segregation of duties among other key areas. In addition, our annual SOC 2 audits focus on security and availability and the results are provided in a SOC 2 Type II report. Trusted and secure providers should make this report available upon request. For additional information, visit our security page. 
2. User security
It’s important to consider not just where your data is stored but also who has access to it. Addressing user security means governing who has access to your data, and to what degree. There are two methods of authentication available within Tableau Online, and you have the flexibility to use one or both of them:
3. Data security and availability
Before uploading your data into a cloud service, it’s important to understand how the data will be secured and what level of granularity is provided. Access to data and workbooks in your site are restricted to those individuals you authorize. You can define additional security in your workbooks and data sources by adding user- and data-source filters. User filters allow you to limit the data any given person can see in a published view. Data-source filters operate in a similar fashion to user filters. Set a filter on a published data source, and it will apply globally.  Keeping your data secure is crucial but so is ensuring you can access it reliably. For disaster recovery, systems are staged at a secondary site to service production traffic should a failover be necessary.
Keeping your data secure is crucial but so is ensuring you can access it reliably. For disaster recovery, systems are staged at a secondary site to service production traffic should a failover be necessary.
4. Application security
Application security is a combination of secure design practices that include defining security requirements, threat modeling, code reviews, and security testing. Additionally, at Tableau, we address application security by working with third-party security experts to test, discover, validate, and address security concerns. 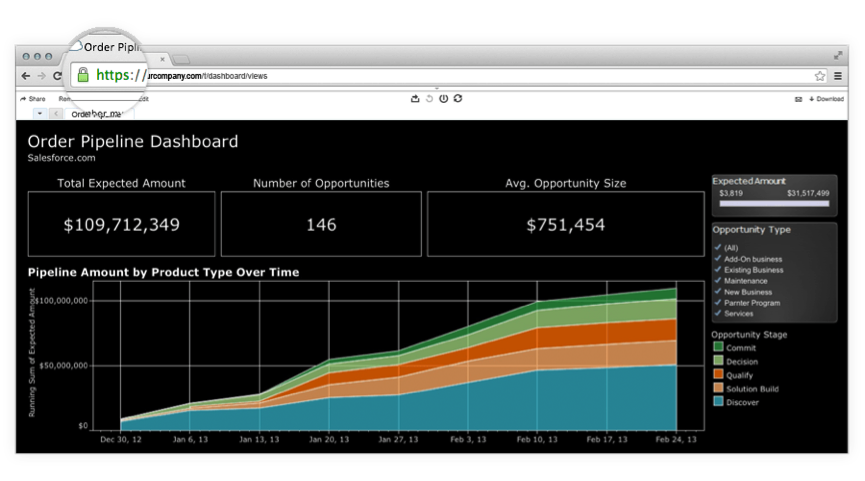 Communication between the client (Tableau Desktop or a supported browser) and Tableau Online is encrypted using TLS, which provides protection of data in transit. In addition, Tableau products have many built-in security mechanisms to help prevent spoofing, hijacking, and SQL injection attacks. Tableau has also implemented a third-party scanning service that continuously scans the service for vulnerabilities. Coupled with our scheduled internal scanning service, we can ensure Tableau Online systems and applications are being checked against the latest threats as they arise. Subscribe to our security bulletins feed for the latest information on product security. To hear more about how our cloud product Tableau Online meets each of these security considerations and more, sign up for our upcoming webinar on security in the cloud.
Communication between the client (Tableau Desktop or a supported browser) and Tableau Online is encrypted using TLS, which provides protection of data in transit. In addition, Tableau products have many built-in security mechanisms to help prevent spoofing, hijacking, and SQL injection attacks. Tableau has also implemented a third-party scanning service that continuously scans the service for vulnerabilities. Coupled with our scheduled internal scanning service, we can ensure Tableau Online systems and applications are being checked against the latest threats as they arise. Subscribe to our security bulletins feed for the latest information on product security. To hear more about how our cloud product Tableau Online meets each of these security considerations and more, sign up for our upcoming webinar on security in the cloud.
And visit our Tableau security page to learn more about this topic.